
Capstone Project — Building a Complete Blog Platform
Project Requirements Review Over the past 17 lectures, you built a blog platform piece by piece — each lecture adding one capability. This final lecture ties everything together into a […]

Project Requirements Review Over the past 17 lectures, you built a blog platform piece by piece — each lecture adding one capability. This final lecture ties everything together into a […]
Building a Production JAR with Maven The Executable JAR Spring Boot packages your entire application — code, dependencies, embedded Tomcat — into a single executable JAR file. This JAR is […]

Identifying Performance Bottlenecks Before optimizing anything, you need to know what is slow. Premature optimization — fixing things that are not problems — wastes time and adds complexity. The 80/20 […]

Testing Pyramid — Unit, Integration, End-to-End Why Test? You have built a blog API with authentication, file uploads, pagination, and relationships. How do you know it works? Manual testing with […]
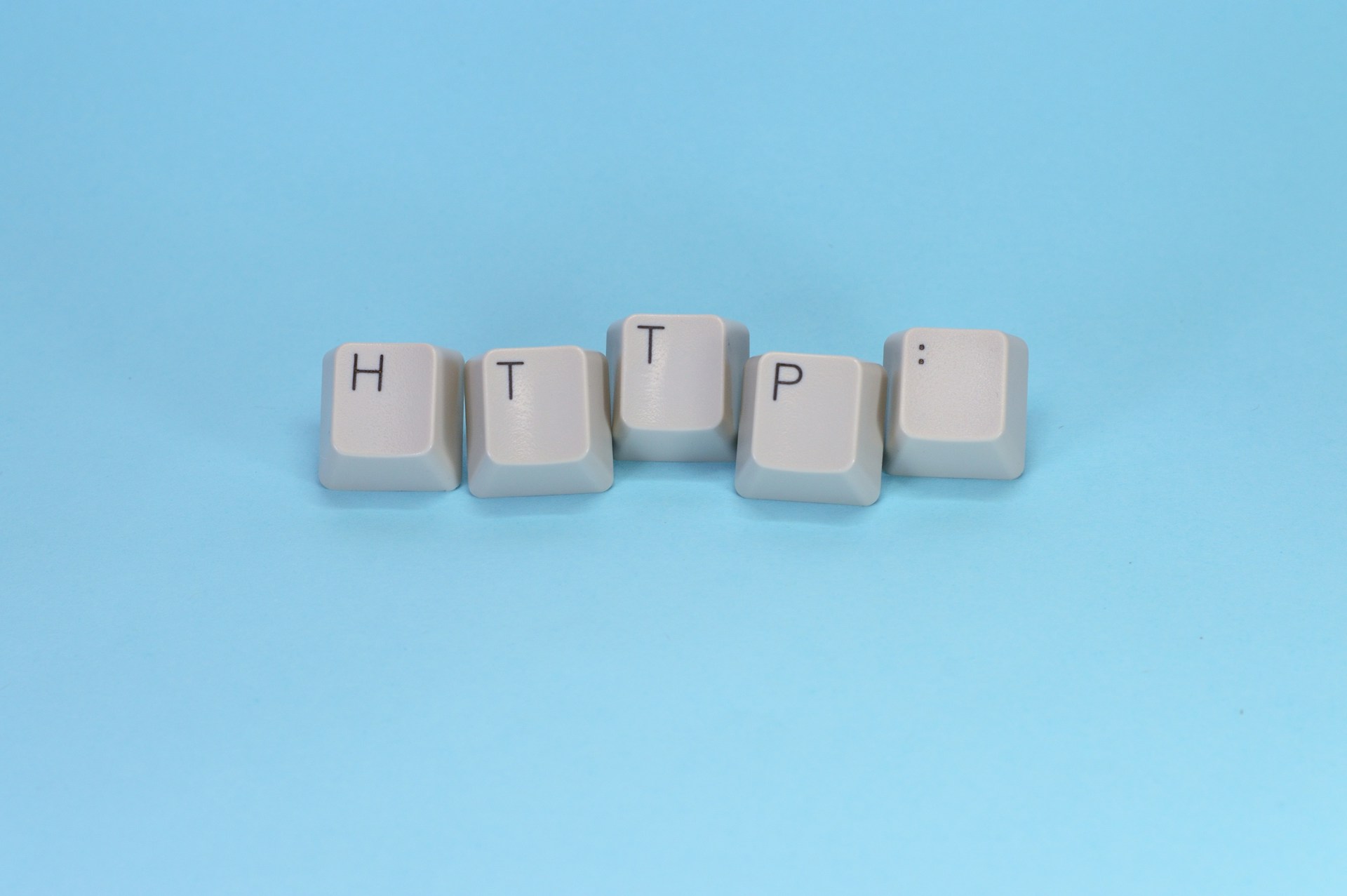
Why API Documentation Matters You have built a fully functional blog API with authentication, file uploads, validation, and pagination. But there is a problem: how does anyone else know how […]
Handling Multipart File Uploads What is a Multipart Request? When a browser or API client uploads a file, it sends the data as a multipart/form-data request. This is a special […]
Session-Based vs Token-Based Authentication In Lecture 11, we configured HTTP Basic authentication. On every request, the client sends the username and password. This works but has a critical flaw: sending […]

Web Security Fundamentals — Authentication vs Authorization Before diving into Spring Security, you need to understand two concepts that form the foundation of all web security. Authentication — “Who are […]

The Problem — Why ddl-auto=update is Dangerous in Production Since Lecture 5, we have been using this configuration: This tells Hibernate: “Compare my entity classes to the database and apply […]

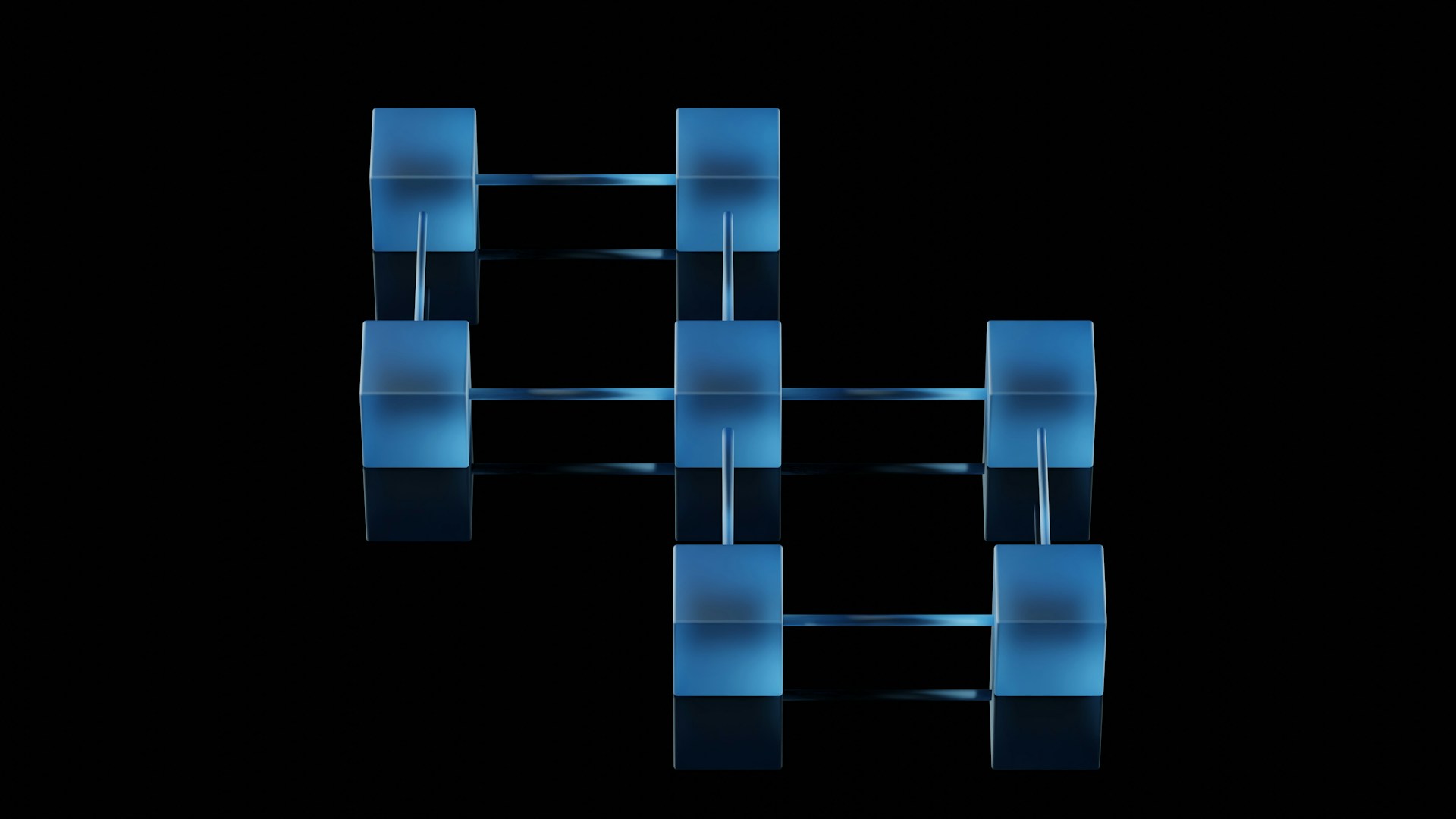
Layered Architecture — Controller → Service → Repository We have been using the layered architecture since Lecture 2, but we have never formally defined the rules that govern each layer. […]